In the world of internet security, there’s often a great deal to be said about the need for ethical hackers or simply security experts across organizations that need the best in security practice and vulnerability discovery that warrants a set of tools that are capable of getting the job done.
Designated systems have been crafted for the job and they are cloud-based, proprietary in nature, or open-source in philosophy. The web variants are effectively countering efforts by malicious players in real-time but don’t do the best in vulnerability discovery or mitigation.
The other categories of proprietary or open-source tools, however, will do a better job with preventing zero-day vulnerabilities provided an ethical hacker is doing the job of staying ahead of the so-called malicious players.
As indicated below, the listed tools will guarantee a safe and secure environment to strengthen your security apparatus in your designated organization. As it’s often referred to, penetration testing will aid the augmentation of a WAF (web application firewall) by orchestrating a simulated attack for exploitable vulnerabilities.
Typically, time is of the essence and a good pen tester will integrate tried and tested methods in carrying out a successful attack. These include external testing, internal testing, blind testing, double-blind testing, and targeted testing.
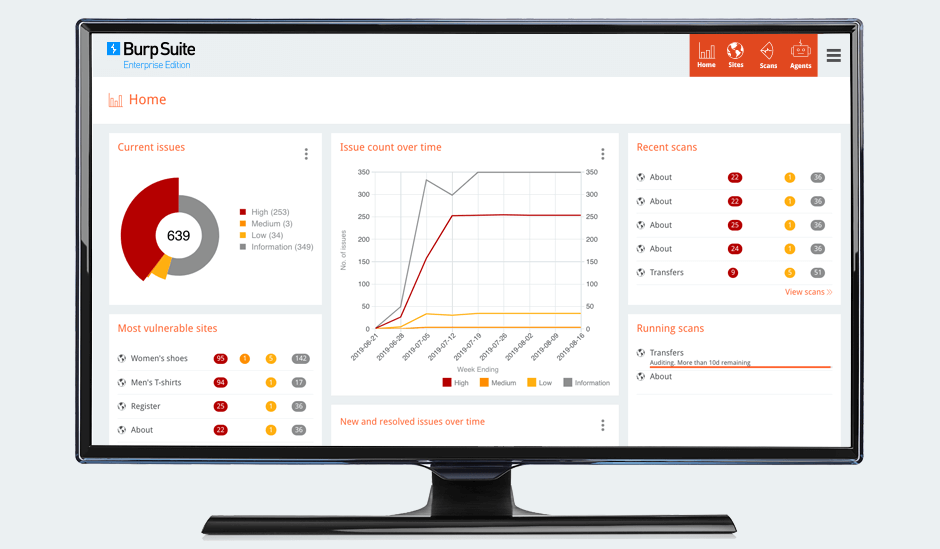
1. Burp Suite (PortSwigger)
With three distinctive packages of enterprise, professional, and community, Burp Suite highlights the advantage of a community-oriented approach to the bare minimum necessary for pentesting.
The community variation of the platform grants end-users access to the basics of web security testing by slowly reeling users into the culture of web security approaches that enhances one’s ability to effect a decent level of control over the basic security needs of a web application.
With their professional and enterprise packages, you can further enhance the capability of your web application firewall.
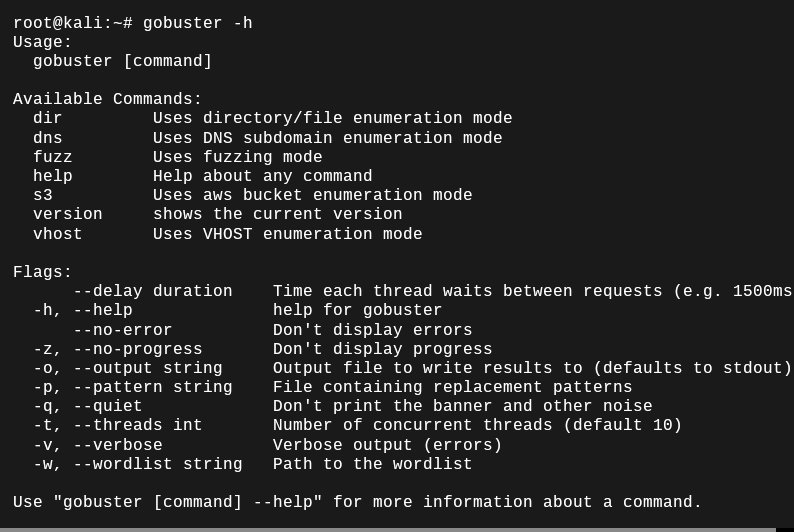
2. Gobuster
As an open-source tool that can be installed on pretty much any Linux operating system, Gobuster is a community favorite considering it’s bundled with Kali Linux (an operating system designated for pentesting). It can facilitate the brute-forcing of URLs, web directories, including DNS subdomains hence its wild popularity.
3. Nikto
Nikto as a pentesting platform is a valid automation machine for the scanning of web services for outdated software systems together with the ability to sniff out issues that may otherwise go unnoticed.
It’s often used in the discoverability of software misconfigurations with the ability to detect server inconsistencies as well. Nikto is open source with the added extra of curtailing security vulnerabilities that you may not be aware of in the first place. Learn more about Niko on their official Github.
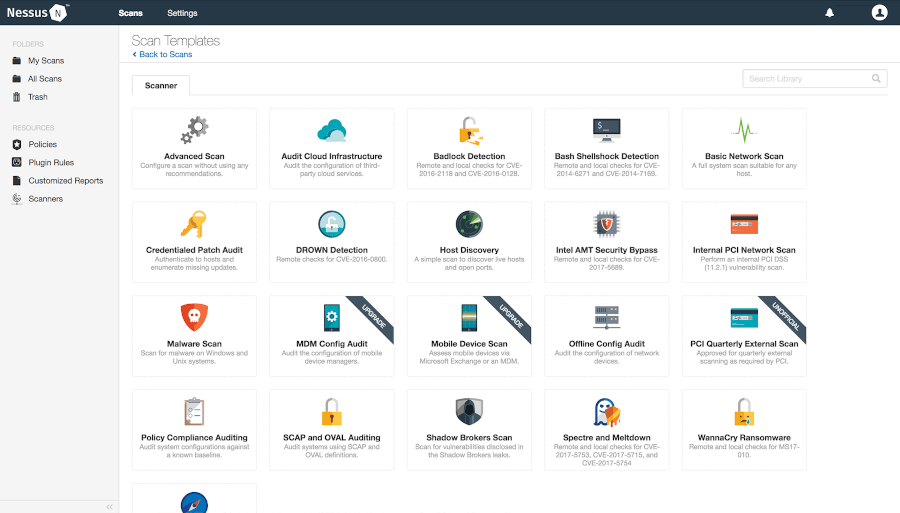
4. Nessus
With over two decades in existence, Nessus has been able to carve a niche out for itself by primarily focusing on vulnerability assessment with an intentional approach to the practice of remote scanning.
With an efficient detection mechanism, it deduces an attack that a malicious actor could use and promptly alerts you to the presence of this vulnerability.
Nessus is available in two different formats Nessus essentials (capped at 16 IPs) and Nessus Professional under its vulnerability assessment focus.
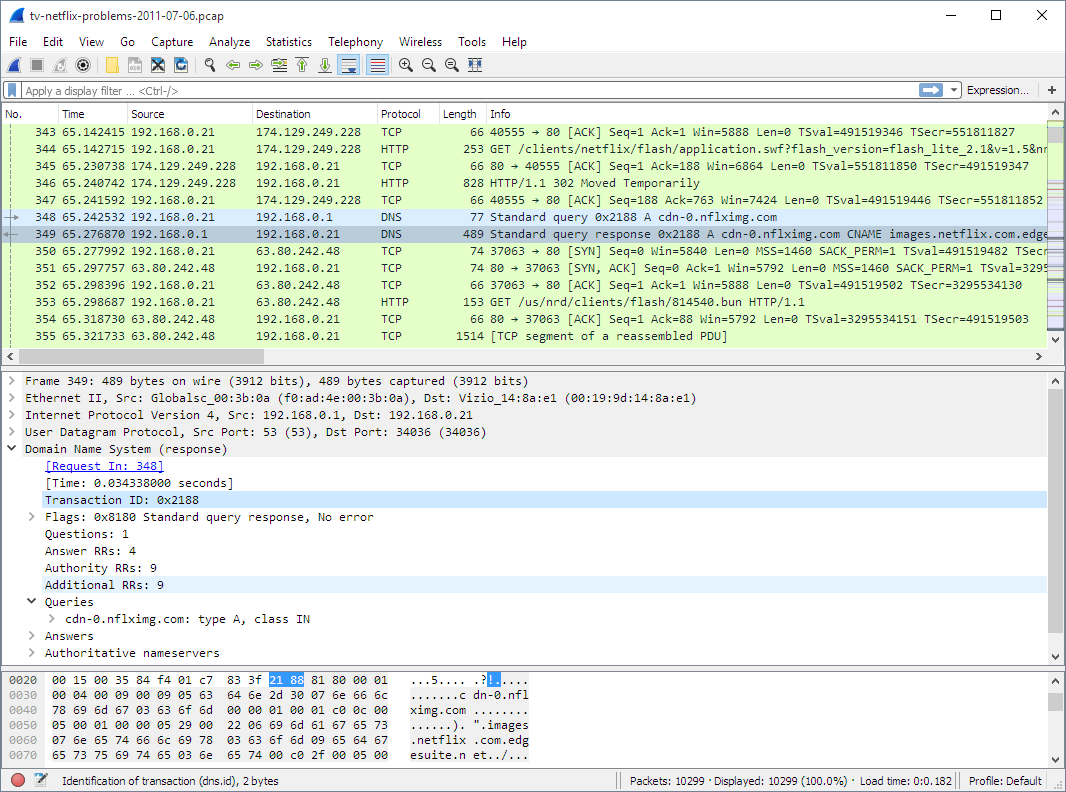
5. Wireshark
The often unsung hero of security, Wireshark has the honor of being generally regarded as the industry standard when it comes to strengthening web security. It does so by being ubiquitous in functionality.
As a network protocol analyzer, Wireshark is an absolute monster in the right hands. Given how it’s used extensively across the board in terms of industries, organizations, and even government institutions, It wouldn’t be far-fetched for me to call it the undisputed champion on this list.
Perhaps where it does falter a bit is in its steep learning curve and this is often the reason why newcomers in the pen testing niche will typically deviate towards other options but those that dare to go in-depth in penetration testing will inevitably come across Wireshark in their career path.
6. Metasploit
As one of the open-source platforms on this list, Metasploit holds its own when it comes to the feature set that enables consistent vulnerability reports amongst other unique forms of security enhancement that will enable the kind of structure you desire for your web server and apps. It serves the majority of platforms out there and can be customized to your heart’s content.
It consistently delivers and this is why it’s often used by both cybercriminals and ethical users alike. It satisfies the majority of the use-cases for both demographics. Considered one of the more stealthy options, it guarantees the kind of vulnerability assessment other players in the pentesting industry advertise.
7. BruteX
With a considerable amount of influence in the pentesting industry, BruteX is a different kind of animal. It combines the power of Hydra, Nmap, and DNSenum all of which are designated tools for pentesting in their own right but with BruteX you get to enjoy the best of all these worlds.
It goes without saying that it automates the entire process using Nmap to scan while forcing the availability of FTP service or SSH service to the effect of a multifunctional brute force tool that drastically reduces your time commitment with the added benefit of being completely open-source as well. Learn more here!
Conclusion
Getting in the habit of utilizing pentesting for your specific server or web app or any other ethical use case is generally regarded as one of the best security practices you should include in your arsenal.
It doesn’t only guarantee foolproof security for your network but gives you the opportunity to discover security holes in your system before a malicious actor does so they may not be zero-day vulnerabilities.
Larger organizations are more inclined to use pentesting tools, however, there’s no limit to what you can accomplish as a small player as well provided you start small. Being security-minded is ultimately the goal here and you shouldn’t take it lightly irrespective of your size as a company.
